Table of Contents
Secure Apache with Let's Encrypt on CentOS 8

Let’s Encrypt is a free, automated, and open certificate authority developed by the Internet Security Research Group (ISRG) that provides free SSL certificates.
Certificates issued by Let’s Encrypt are trusted by all major browsers and valid for 90 days from the issue date.
This tutorial explains how to install a free Let’s Encrypt SSL certificate on CentOS 8 running Apache as a web server. We’ll use the certbot tool to obtain and renew the certificates.
Installation Tutorial
Prerequisites
Ensure that the following prerequisites are met before continuing:
- Have a domain name pointing to your public server IP. We’ll use example.com.
- Apache is installed and running on your server with a virtual host configured for your domain.
- Ports 80 and 443 are open in your firewall.
Install the following packages which are required for an SSL encrypted web server:
# dnf install mod_ssl openssl
When the mod_ssl package is installed, it should create a self-signed key and certificate files for the localhost. If the files are not automatically created, you can create them using the openssl command:
# openssl req -newkey rsa:4096 -x509 -sha256 -days 3650 -nodes \ -out /etc/pki/tls/certs/localhost.crt \ -keyout /etc/pki/tls/private/localhost.key
Install Certbot
Certbot is a free command-line tool that simplifies the process for obtaining and renewing Let’s Encrypt SSL certificates from and auto-enabling HTTPS on your server.
The certbot package is not included in the standard CentOS 8 repositories, but it can be downloaded from the vendor’s website.
Run the following wget command as root or sudo user to download the certbot script to the /usr/local/bin directory:
# wget -P /usr/local/bin https://dl.eff.org/certbot-auto
Once the download is complete, make the file executable:
# chmod +x /usr/local/bin/certbot-auto
Generate Strong Dh (Diffie-Hellman) Group
Diffie–Hellman key exchange (DH) is a method of securely exchanging cryptographic keys over an unsecured communication channel. Generate a new set of 2048 bit DH parameters to strengthen the security:
# openssl dhparam -out /etc/ssl/certs/dhparam.pem 2048
You can change the size up to 4096 bits, but the generation may take more than 30 minutes depending on the system entropy.
Obtaining a Let’s Encrypt SSL certificate
To obtain an SSL certificate for the domain we’re going to use the Webroot plugin that works by creating a temporary file for validating the requested domain in the ${webroot-path}/.well-known/acme-challenge directory. The Let’s Encrypt server makes HTTP requests to the temporary file to validate that the requested domain resolves to the server where certbot runs.
To make the setup more simple we’re going to map all HTTP requests for .well-known/acme-challenge to a single directory, /var/lib/letsencrypt.
Run the following commands to create the directory and make it writable for the Apache server.
# mkdir -p /var/lib/letsencrypt/.well-known # chgrp apache /var/lib/letsencrypt # chmod g+s /var/lib/letsencrypt
To avoid duplicating code and make the configuration more maintainable, create the following two configurations snippets:
# vim /etc/httpd/conf.d/letsencrypt.conf
Alias /.well-known/acme-challenge/ "/var/lib/letsencrypt/.well-known/acme-challenge/"
<Directory "/var/lib/letsencrypt/">
AllowOverride None
Options MultiViews Indexes SymLinksIfOwnerMatch IncludesNoExec
Require method GET POST OPTIONS
</Directory>
# vim /etc/httpd/conf.d/ssl-params.conf
SSLCipherSuite EECDH+AESGCM:EDH+AESGCM # Requires Apache 2.4.36 & OpenSSL 1.1.1 SSLProtocol -all +TLSv1.3 +TLSv1.2 SSLOpenSSLConfCmd Curves X25519:secp521r1:secp384r1:prime256v1 # Older versions # SSLProtocol All -SSLv2 -SSLv3 -TLSv1 -TLSv1.1 SSLHonorCipherOrder On Header always set Strict-Transport-Security "max-age=63072000; includeSubDomains; preload" Header always set X-Frame-Options DENY Header always set X-Content-Type-Options nosniff # Requires Apache >= 2.4 SSLCompression off SSLUseStapling on SSLStaplingCache "shmcb:logs/stapling-cache(150000)" # Requires Apache >= 2.4.11 SSLSessionTickets Off SSLOpenSSLConfCmd DHParameters "/etc/ssl/certs/dhparam.pem"
The snippet above is using the chippers recommended by Cipherli.st. It enables OCSP Stapling, HTTP Strict Transport Security (HSTS), Dh key, and enforces few security‑focused HTTP headers.
Reload the Apache configuration for changes to take effect:
# systemctl reload httpd
Now, you can run certbot script with the webroot plugin and fetch the SSL certificate files:
# /usr/local/bin/certbot-auto certonly --agree-tos --email admin@example.com --webroot -w /var/lib/letsencrypt/ -d example.com -d www.example.com
On success, certbot will print the following message:
IMPORTANT NOTES: - Congratulations! Your certificate and chain have been saved at: /etc/letsencrypt/live/example.com/fullchain.pem Your key file has been saved at: /etc/letsencrypt/live/example.com/privkey.pem Your cert will expire on 2020-01-26. To obtain a new or tweaked version of this certificate in the future, simply run certbot-auto again. To non-interactively renew *all* of your certificates, run "certbot-auto renew" - Your account credentials have been saved in your Certbot configuration directory at /etc/letsencrypt. You should make a secure backup of this folder now. This configuration directory will also contain certificates and private keys obtained by Certbot so making regular backups of this folder is ideal. - If you like Certbot, please consider supporting our work by: Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate Donating to EFF: https://eff.org/donate-le
Include certificates in apache to Encrypt traffic
Now that everything is set up, edit your domain virtual host configuration as follows:
# vim /etc/httpd/conf.d/example.com.conf
<VirtualHost *:80>
ServerName example.com
ServerAlias www.example.com
Redirect permanent / https://example.com/
</VirtualHost>
<VirtualHost *:443>
ServerName example.com
ServerAlias www.example.com
Protocols h2 http:/1.1
<If "%{HTTP_HOST} == 'www.example.com'">
Redirect permanent / https://example.com/
</If>
DocumentRoot /var/www/example.com/public_html
ErrorLog /var/log/httpd/example.com-error.log
CustomLog /var/log/httpd/example.com-access.log combined
SSLEngine On
SSLCertificateFile /etc/letsencrypt/live/example.com/fullchain.pem
SSLCertificateKeyFile /etc/letsencrypt/live/example.com/privkey.pem
# Other Apache Configuration
</VirtualHost>
The configuration above is forcing HTTPS and redirecting from www to non-www version. It also enables HTTP/2, which will make your sites faster and more robust. Fell free to adjusts the configuration according to your needs. Restart the Apache service:
# systemctl restart httpd
You can now open your website using your browser, and you’ll notice a green lock icon.
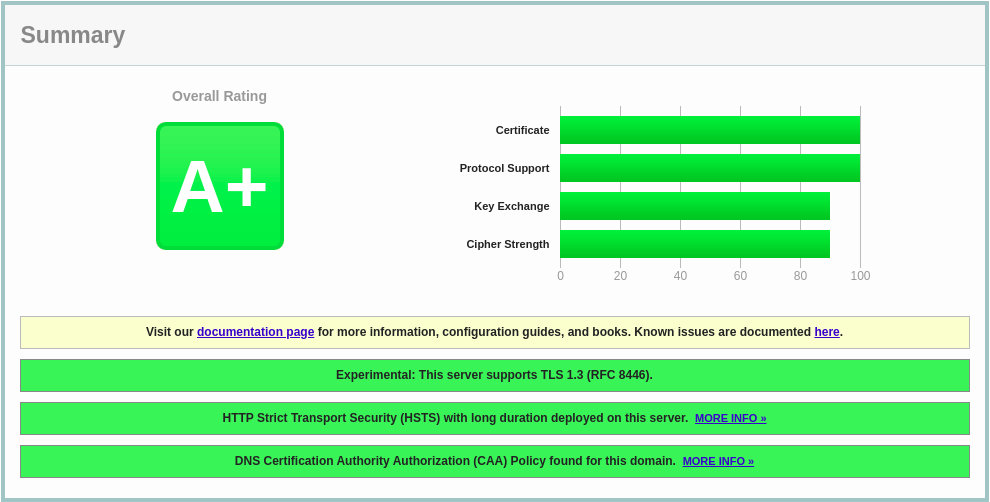
If you test your domain using the SSL Labs Server Test, you’ll get an A+ grade, as shown below:
Auto-renewing Let’s Encrypt SSL certificate
Let’s Encrypt’s certificates are valid for 90 days. To automatically renew the certificates before they expire, we’ll create a cronjob that will run twice a day and automatically renew any certificate 30 days before its expiration.
Run the following command to create a new cronjob which will renew the certificate and restart Apache:
# echo "0 0,12 * * * root python3 -c 'import random; import time; time.sleep(random.random() * 3600)' && /usr/local/bin/certbot-auto -q renew --renew-hook \"systemctl reload httpd\"" | sudo tee -a /etc/crontab > /dev/null
To test the renewal process, use the certbot command followed by the –dry-run switch:
# /usr/local/bin/certbot-auto renew --dry-run
If there are no errors, it means that the renewal process was successful.